The Rise of Progz: How Script Kiddies Conquered 90s Chat Rooms
It's 11:47 PM on a school night in 1998. You're sitting in front of a beige Compaq Presario, bathed in the blue-white glow of a 15-inch CRT monitor. Your 56k modem just finished its symphony of screeches and hisses - that beautiful handshake - and you're connected. You double-click a small executable called YahooBooter_v3.2.exe that you downloaded from a Geocities page with a black background, green text, and an animated flaming skull GIF. Norton Antivirus pops up a warning. You click "Ignore." You always click ignore.
You paste a Yahoo username into the target field, click the button labeled "BOOT" in bold red Comic Sans, and somewhere across the internet, a stranger gets disconnected from their chat room mid-sentence. You feel like a god. You are fourteen years old.
This is the story of progz - the small, crude, often malicious programs that defined an entire underground subculture of the late 1990s internet. It's a story about teenagers who taught themselves to code by building tools to terrorize chat rooms. It's about Yahoo Chat and AOL and IRC and the wild, lawless frontier of the early web. It's about Visual Basic 6, Winsock controls, Geocities pages, and a generation of kids who stumbled into computer science through the back door of digital mischief.
This is a love letter to a lost era. Not because what we did was right - most of it was obnoxious at best and illegal at worst - but because it was real, it was formative, and for many of us, it was the spark that lit a lifelong career in technology.
1. The Scene: Welcome to the Wild West
The late 1990s desktop: a beige tower, a CRT monitor, and a world of possibilities hiding behind a dial-up connection.
To understand progz, you have to understand the internet of the late 1990s. It was nothing like today. There was no Facebook, no Twitter, no Instagram, no TikTok, no YouTube. Google was a research project at Stanford. Amazon sold books. The internet was a frontier - vast, unregulated, and thrillingly anonymous.
Most Americans connected through one of three gateways: AOL (America Online), which was less an ISP and more a walled garden with its own chat rooms, instant messaging, and keyword system; Yahoo, which offered free email, a web directory, and - crucially - a massive chat room network; or a local ISP that gave you a raw dial-up PPP connection and left you to figure out the rest.
The connection itself was an experience. You'd pick up the phone (yes, the actual telephone - internet and phone shared the same line), hear the dial tone, then launch your dialer. The modem would screech and warble through its handshake protocol - a sound so iconic that anyone who lived through it can still hear it in their mind. If someone picked up the phone extension in another room, your connection died. If your mom needed to make a call, your connection died. If a strong wind blew, your connection died. You were perpetually one phone call away from disconnection, and your bandwidth topped out at 56 kilobits per second - roughly 7 kilobytes per second on a good day. Loading a single JPEG could take thirty seconds.
But none of that mattered, because what waited on the other end was magic.
The Chat Room as Social Space
Before social media, before forums went mainstream, before Discord and Slack and every other modern communication platform, there were chat rooms. Real-time, text-based, chaotic, beautiful chat rooms. And they were everywhere.
Yahoo Chat alone hosted thousands of rooms organized by category: Romance, Music, Sports, Computers & Internet, Regional rooms for every state and major city, age-based rooms like "20-Something" and "30-Something," and user-created rooms for every conceivable interest and several inconceivable ones. At peak hours in the late '90s, Yahoo Chat had hundreds of thousands of simultaneous users. It was the town square of the internet.
AOL had its own parallel universe of chat rooms - "People Connection" was the hub, with rooms organized by topic and region. AOL's chat rooms were arguably even more culturally significant because AOL was many Americans' first experience with the internet. When you heard "You've Got Mail," you were already inside AOL's ecosystem, and the chat rooms were just a click away.
And then there was IRC - Internet Relay Chat. If Yahoo and AOL were the shopping malls of online chat, IRC was the back alley. IRC was decentralized, running across networks like EFnet, DALnet, Undernet, and QuakeNet. It required a dedicated client (mIRC was the gold standard on Windows), and it had no corporate oversight. IRC was where the technically inclined gathered, where open-source projects coordinated, where warez groups distributed pirated software, and where the hacker underground thrived.
Teenagers and the Thrill of the Underground
Into this landscape walked millions of teenagers. We were the first generation to grow up with home computers and internet access, and we were largely unsupervised online. Our parents didn't understand the internet - many of them could barely check email. There were no parental controls worth mentioning, no content filters, no monitoring software. We were digital natives before the term existed, and we were curious.
The thrill wasn't just about chat rooms. It was about the realization that software could be manipulated. That protocols had weaknesses. That the systems we used every day were held together with duct tape and good intentions. And that with the right tool - the right prog - you could exploit those weaknesses to do things you weren't supposed to do.
For a teenager in 1998, discovering that you could disconnect someone from a chat room with a small program felt like discovering a superpower. It was intoxicating. It was addictive. And it was the gateway drug to a lifetime of fascination with how computers actually work.

The hacker aesthetic: dark rooms, glowing screens, and the feeling that you were part of something secret.

Late nights in front of the CRT - this was where the magic happened.
The platforms that defined the era: GeoCities, ICQ, and AIM - logos via Wikimedia Commons (public domain)
2. What Were Progz?

Code was power - even if most progz users never read a single line of it.
"New Wave" - a real VB6 Remote Administration Tool from 2001, built for ICQ-era remote access
The word "progz" was simply slang for "programs" - spelled with a 'z' because in the late '90s underground, replacing 's' with 'z' was the height of cool. But in practice, "progz" referred to a very specific category of software: small Windows executables designed to exploit vulnerabilities in chat room platforms, primarily Yahoo Messenger, AOL, and IRC clients.
These weren't sophisticated hacking tools. They weren't written by security researchers or intelligence agencies. Most of them were written by teenagers - 14, 15, 16-year-old kids who had taught themselves Visual Basic 6 or Delphi and figured out how to send malformed packets to Yahoo's chat servers. The code was often terrible. The user interfaces were worse. But they worked, and that was all that mattered.
The Anatomy of a Prog
A typical prog was a Windows executable, usually between 200KB and 2MB in size. It had a gray Windows form (the default VB6 look) with a collection of text fields, buttons, and maybe a few labels in bold colored fonts. The aesthetic was unmistakable: Comic Sans or MS Sans Serif, bright red or green text on a gray background, buttons labeled with aggressive verbs like "BOOT," "FLOOD," "JACK," and "BOMB."
Under the hood, most progz worked by exploiting weaknesses in the Yahoo Chat protocol (YMSG), AOL's OSCAR protocol, or IRC's relatively open architecture. They used the Winsock control - a Visual Basic component that provided access to TCP/IP sockets - to send raw network packets to chat servers. The exploits were usually simple: send a malformed packet that the server doesn't handle gracefully, and the target user gets disconnected. Send enough packets fast enough, and you can flood an entire room. Spoof the right headers, and you can impersonate other users.
The names were legendary in their bluntness:
- Yahoo Booter - Disconnects a user from Yahoo Chat
- Mass Punter - Disconnects everyone in a room simultaneously
- Room Jacker - Takes control of a chat room
- Chat Bomber - Floods a room with repeated messages
- Mail Bomber - Floods an email inbox with thousands of messages
- Name Stealer - Hijacks desirable Yahoo usernames
- Webcam Capper - Captures webcam feeds without consent
- Voice Bomber - Disrupts Yahoo voice chat with noise
Every prog came with a risk. Because they exploited network protocols and often contained code that antivirus software flagged as malicious, downloading and running progz was an act of faith. You were trusting that the anonymous teenager who coded this thing and uploaded it to a Geocities page with a visitor counter and a "Best Viewed in Netscape Navigator" badge hadn't also included a trojan that would steal your passwords. Spoiler: they often had.
The Progz Ecosystem
Progz didn't exist in isolation. They were part of a broader ecosystem that included:
- Prog sites - Geocities, Angelfire, and Tripod pages dedicated to hosting progz downloads
- Prog crews - Groups of coders who collaborated on tools and competed for reputation
- Prog forums - Message boards where users shared tools, exploits, and bragging rights
- IRC channels - Where the more technically inclined gathered to trade code and techniques
- Yahoo rooms - Where the progz were actually used, turning chat rooms into digital battlefields
The scene had its own vocabulary, its own hierarchy, its own culture. And at the center of it all was one platform that served as both the stage and the target: Yahoo Chat.

Actual Yahoo Messenger banner, circa 2005 - recovered from the Wayback Machine
3. Yahoo Chat Room Culture: The Town Square of the Internet
Before social media, before dating apps, before Discord - there were Yahoo Chat rooms.
If you weren't there, it's hard to convey just how central Yahoo Chat was to late-'90s internet culture. It wasn't just a feature of Yahoo - it was a destination. Millions of people logged in every day to talk to strangers, flirt, argue, role-play, and yes, harass each other. It was messy, chaotic, often toxic, and utterly addictive.
The Room Structure
Yahoo Chat was organized into categories and subcategories, each containing dozens or hundreds of rooms. The main categories included:
- Romance - The most populated category by far. Rooms like "Romance," "Romance 2," all the way up to "Romance 20+" during peak hours. This was proto-Tinder, except everyone was anonymous and lying about their age.
- Regional - Rooms for every US state and major city. "Texas," "California," "New York City." These were where you'd find people who actually wanted to meet up in real life.
- Age-Based - "20-Something," "30-Something," "40-Something." The age verification was nonexistent, so a "20-Something" room might contain anyone from 13 to 60.
- Computers & Internet - Where the tech-savvy gathered. Also where progz users went to show off and recruit.
- Music - Genre-specific rooms. The rap rooms and metal rooms had their own distinct cultures.
- Lobby - The default room you landed in. Pure chaos. The Lobby was a firehose of "a/s/l?" (age/sex/location), spam, and progz attacks.
Each room could hold up to 50 users (later expanded). When a room filled up, Yahoo automatically created a new instance - "Romance:1," "Romance:2," and so on. During peak evening hours, popular categories could have dozens of overflow rooms, each packed to capacity.
The Social Dynamics
Every Yahoo Chat room developed its own micro-society. The social hierarchy was remarkably consistent:
- Regulars - People who showed up in the same room every night. They knew each other, had inside jokes, and formed genuine friendships (and sometimes relationships). Regulars were the backbone of any room's culture.
- Room Creators/Ops - Users who created custom rooms had limited moderation powers. They could set the room topic and, in some cases, boot disruptive users. Being a room op was a status symbol.
- Newbies - Fresh arrivals who didn't know the room's culture. They'd get hazed, ignored, or welcomed depending on the room's vibe.
- Trolls - People who showed up specifically to provoke reactions. Trolling in Yahoo Chat was an art form - the best trolls could derail an entire room's conversation with a single well-placed comment.
- Progz Users - The nuclear option. When a progz user entered a room, the dynamic shifted immediately. They could boot anyone, flood the room, or crash the entire session. They were feared, hated, and secretly envied.
The Language of Yahoo Chat
Yahoo Chat had its own dialect. If you were there, you remember:
- a/s/l? - Age/Sex/Location. The universal opening line. Everyone asked it. Everyone lied in response.
- brb - Be right back. Usually meant "my mom picked up the phone and killed my connection."
- pm me - Private message me. The transition from public chat to private conversation was where things got interesting (and often creepy).
- lol, rofl, lmao - These weren't just abbreviations; they were the birth of the texting language that would later dominate mobile communication.
- cyber - Short for "cybersex." Yes, this was a thing. A very, very common thing. Entire rooms were dedicated to it.
- boot/punt - To disconnect someone. "I'll boot you" was the chat room equivalent of a threat.
- prog me - A request (or demand) for someone to share their progz.
The Chat Room as Battlefield
When progz entered the picture, Yahoo Chat rooms became war zones. A typical evening might go like this:
You're in "20-Something:3," having a normal conversation with the regulars. Someone new joins - their username is something like "xX_DarkLord_Xx" or "BoOtEr_KiNg_99." Within seconds, people start getting disconnected. The room floods with repeated lines of text or ASCII art. Someone's webcam feed gets captured and reposted. The room creator tries to boot the attacker, but the attacker has multiple accounts and keeps rejoining. Within five minutes, the room is destroyed - all the regulars have fled to a different room or logged off entirely.
This happened constantly. Every single night. In every popular room. It was the defining experience of Yahoo Chat in its later years, and it was one of the primary reasons the platform eventually died. Yahoo couldn't (or wouldn't) fix the underlying protocol vulnerabilities, and users eventually got tired of the constant disruption and migrated to other platforms.
But for the progz users? It was the greatest game ever invented. Every room was a new conquest. Every booted user was a trophy. Every crashed room was a victory. The dopamine hit of watching a room full of people scatter because of something you did was irresistible to a teenager with too much free time and not enough supervision.
The actual Yahoo Chat banner from 1998 - pulled from the Wayback Machine archive of chat.yahoo.com
Yahoo Chat actions menu (archived 2000) - this is where the chaos happened

Yahoo Chat badge
💾 The Real Progz - Actual Screenshots
These aren't recreations. These are actual screenshots of the tools that ruled Yahoo and AOL chat rooms.
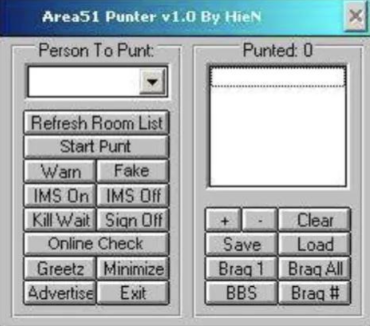
Area51 Punter v1.0 by HieN - a real Yahoo chat room punter. Note the classic VB6 gray form, "Person To Punt" dropdown, "Punted: 0" counter, and buttons like "Start Punt", "Warn", "Fake", "Kill Wait", "Greetz", and "Braq All". This is EXACTLY what progz looked like.
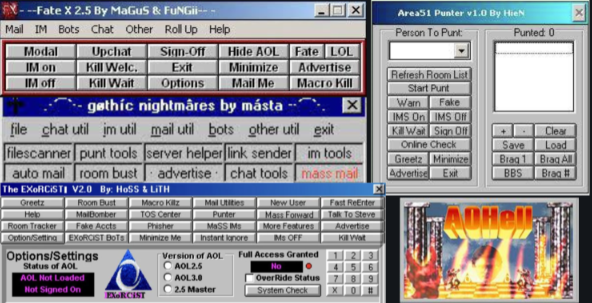
The progz scene in one screenshot: Fate X 2.5 by MaGuS & FuNGii (top left), Area51 Punter (top right), Gothic Nightmares by másta (middle), The Exorcist V2.0 by HoSS & LiTH (bottom left), and AOHell (bottom right). Tools include Room Bust, MailBomber, TOS Center, Punter, Mass Forward, Macro Killz, filescanner, punt tools, server helper, link sender, and more.
4. The Progz Arsenal: A Complete Breakdown
The progz scene wasn't monolithic - it was a diverse ecosystem of specialized tools, each designed to exploit a different aspect of chat room platforms. Here's a detailed breakdown of every major category of prog, how they worked, and why they mattered.
Booters & Punters

Somewhere in a server room like this, Yahoo's chat servers were getting hammered by thousands of teenagers with booter programs.
Booters (also called punters) were the bread and butter of the progz scene. Their function was simple: disconnect a target user from Yahoo Chat. The mechanism varied over time as Yahoo patched exploits and progz authors found new ones, but the general approach was consistent.
Early booters exploited the YMSG (Yahoo Messenger) protocol directly. Yahoo's chat system communicated using a proprietary binary protocol over TCP. Booters would send specially crafted packets to Yahoo's servers that triggered bugs in how the server handled user sessions. Some exploits caused the server to send a disconnect command to the target. Others caused the target's client to crash by sending malformed data that Yahoo Messenger couldn't parse.
The most common technique was the conference invite bomb. Yahoo Messenger had a conference (group chat) feature, and the protocol for inviting users to conferences had weak validation. A booter could send hundreds of conference invitations per second to a target user, overwhelming their client and causing it to freeze or crash. The target would have to close Yahoo Messenger and reconnect - if they could even get back in before the booter targeted them again.
Mass booters took this a step further by targeting every user in a room simultaneously. They'd enumerate the room's user list (which was publicly available through the YMSG protocol) and then boot each user in rapid succession. A skilled mass booter operator could clear a 50-person room in under ten seconds.
Room Jackers
Room jackers were the progz equivalent of a hostile takeover. Yahoo allowed users to create custom chat rooms, and the room creator had limited administrative powers. Room jackers exploited this by using multiple bot accounts to flood a room, overwhelming the legitimate users and effectively taking control.
The technique was straightforward: the jacker would have dozens (sometimes hundreds) of pre-registered Yahoo accounts. The prog would log into all of these accounts simultaneously and join the target room. Since rooms had a user limit, the flood of bots would push out legitimate users. Once the bots controlled the room, the jacker could set the topic, control who stayed, and use the room for whatever purpose they wanted - usually to advertise their prog site or crew.
Some advanced room jackers could exploit Yahoo's room creation protocol to "steal" a room name entirely, replacing the original room with their own version. This was particularly devastating for rooms that had built up a community of regulars over months or years.
Chat Bombers & Flooders
Chat bombers (also called flooders) were the blunt instruments of the progz world. Their function was simple: spam a chat room with so much text that normal conversation became impossible. The text could be anything - repeated phrases, ASCII art, color-coded gibberish, or offensive content.
Yahoo Chat supported basic HTML formatting in messages - bold, italic, color, and font size. Flooders exploited this by sending messages with maximum font sizes and bright colors, making each spam message take up as much screen real estate as possible. A single flood message with <font size="25" color="red"> tags could fill an entire chat window.
The more sophisticated flooders used ASCII art bombs - pre-made ASCII art (skulls, middle fingers, crew logos) that would scroll the chat window so fast that legitimate messages were instantly buried. Some flooders could send hundreds of messages per second, effectively making the room unusable.
Macro Programs
Macro programs were the Swiss Army knives of the progz world. Rather than focusing on a single exploit, macros automated a wide range of chat room actions:
- Auto-greet - Automatically welcomed users who joined the room with a customizable message
- Auto-insult - Automatically sent insults to specific users or anyone who spoke
- Auto-boot - Automatically booted anyone who joined the room (except whitelisted users)
- Auto-respond - Triggered responses based on keywords in chat messages
- Room guard - Combined auto-boot with user whitelisting to "protect" a room from unwanted visitors
Macros turned a single user into an automated chat room overlord. A well-configured macro program could run a room 24/7 without human intervention, greeting friends, booting enemies, and maintaining order (or chaos, depending on the operator's intentions).
Name Stealers
Name stealers exploited weaknesses in Yahoo's account system to hijack desirable usernames. In the late '90s, a good Yahoo username was a status symbol. Short names, real words, and cool-sounding handles were highly coveted. Name stealers used various techniques to gain access to these accounts:
- Security question brute-forcing - Yahoo's password recovery relied on security questions with predictable answers
- Cookie theft - Stealing Yahoo authentication cookies through various exploits
- Social engineering - Tricking users into revealing their passwords through fake Yahoo login pages
- Password list attacks - Trying common passwords against target accounts
Stolen accounts were traded like currency in the progz scene. A one-word Yahoo username could be worth dozens of lesser accounts. The account trading economy was surprisingly sophisticated, with escrow services, reputation systems, and even dedicated trading rooms on IRC.
Webcam Cappers
Webcam cappers were among the most invasive progz. Yahoo Messenger included a webcam feature that allowed users to broadcast video to others. Cappers exploited the protocol to capture these video feeds without the broadcaster's knowledge or consent, saving screenshots or recordings.
The technical exploit was relatively simple: Yahoo's webcam protocol transmitted video data with minimal authentication. A capper could connect to a user's webcam stream by sending the right protocol commands, even if the user hadn't explicitly shared their webcam with the capper. Some cappers could view webcam feeds from users who thought their camera was turned off.
This was, without question, the most ethically reprehensible category of progz. While booting and flooding were annoying, webcam capping was a genuine invasion of privacy. Many victims were unaware their feeds were being captured and shared.
Voice Bombers
When Yahoo added voice chat capabilities to its rooms, the progz scene adapted immediately. Voice bombers disrupted voice chat rooms by flooding the audio channel with noise - loud music, static, offensive audio clips, or simply holding an open microphone next to a speaker playing feedback. Some voice bombers could exploit the voice protocol to transmit audio at maximum volume, overriding other speakers.
Mail Bombers
Mail bombers predated the Yahoo Chat progz scene and were one of the oldest categories of internet harassment tools. They worked by sending thousands of emails to a target address, filling up their inbox and making it unusable. In the era of limited email storage (Yahoo Mail initially offered just 4MB of storage), a mail bomb could effectively shut down someone's email account.
Mail bombers typically used open SMTP relays - mail servers that would accept and forward email from anyone without authentication. In the late '90s, open relays were everywhere, and mail bombers could send thousands of messages through them without any trace back to the sender.
The Famous Progz: A Reference Table
| Prog Name | Type | Platform | Description |
|---|---|---|---|
| Yahoo Booter Pro | Booter | Yahoo | The classic single-target booter. Paste a username, click boot. Simple and effective. |
| Mass Punter | Mass Booter | Yahoo | Booted every user in a room simultaneously. The nuclear option. |
| Room Jacker Elite | Room Jacker | Yahoo | Multi-account room takeover tool with bot management. |
| Chat Bomber 2000 | Flooder | Yahoo | Text and ASCII art flooder with customizable payloads. |
| Super Mail Bomber | Mail Bomber | Sent thousands of emails via open SMTP relays. | |
| AOHell | Multi-tool | AOL | The legendary all-in-one AOL exploitation suite. Phishing, punting, mail bombing, and more. |
| Fate X | Multi-tool | AOL | AOL progz suite with IM bombing, chat room tools, and account phishing. |
| Yahoo Webcam Viewer | Webcam Capper | Yahoo | Captured webcam feeds from Yahoo Messenger users. |
| Y! Toolkit | Multi-tool | Yahoo | All-in-one Yahoo prog with booter, flooder, room tools, and macros. |
| SubSeven | RAT/Trojan | Windows | Remote access trojan often bundled with progz. Gave the attacker full control of the victim's PC. |

mIRC banner ad - the IRC client that launched a thousand script kiddies

mIRC's CNET award badge - legitimacy for an underground tool

The actual Visual Basic product banner from Microsoft's MSDN site (archived 2002) - VB6 was THE language of the progz scene
5. The Visual Basic 6 Era: Where Script Kiddies Learned to Code

Writing code - even bad code - was the gateway to understanding how computers actually worked.
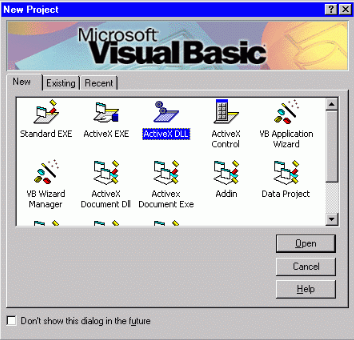
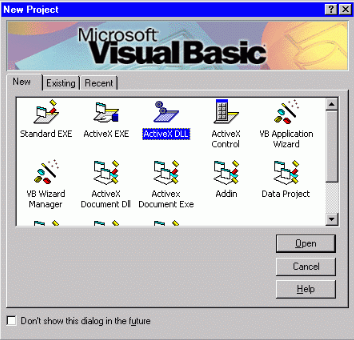
The Visual Basic 6.0 "New Project" dialog - every progz started here. Click "Standard EXE" and you were on your way to building a booter. This is the actual VB6 IDE that powered the entire progz scene.
🖥️ Real Progz Screenshots - From the Era
These are actual screenshots of "New Wave" - a Remote Administration Tool (RAT) built in Visual Basic 6, circa 2001. Recovered from an archived progz distribution page on 50megs.com. This is exactly what the VB6 progz scene looked like.
"New Wave" RAT - a VB6 remote access tool from the progz era, used for ICQ-based remote administration.
New Wave RAT - a full VB6 Remote Administration Tool. This is an actual screenshot from 2001. Note the classic gray VB6 form, command buttons, and tabbed interface. This is EXACTLY what progz looked like.
New Wave - connection panel. Classic VB6 gray forms with command buttons.
New Wave - another panel. Note the typical VB6 UI elements of the era.
About these screenshots: These images come from an actual progz distribution page hosted on 50megs.com (a free web host popular in the early 2000s). The site offered downloads of a Remote Administration Tool called "New Wave" alongside Yahoo Boot tools - all written in Visual Basic 6. RATs like New Wave let users remotely control another person's computer over ICQ or direct IP connections. The site was "Made in Notepad" and had a 7-segment hit counter. This was the authentic progz scene.
Classic 7-segment hit counter from the original page:




"Hits since March, 2001" - the actual hit counter from the progz page

The VB6 IDE was many teenagers' first encounter with a real development environment.
If progz were the weapons, Visual Basic 6 was the forge. Released by Microsoft in 1998, VB6 was never intended to be a hacking tool. It was designed as a rapid application development (RAD) environment for building Windows business applications. But its accessibility, its power, and its timing made it the de facto programming language of the progz scene.
Why VB6 Was Perfect
VB6 hit a sweet spot that no other language of the era could match:
- Visual form designer - You could drag and drop buttons, text fields, and labels onto a form. No need to write GUI code by hand. For a teenager who had never programmed before, seeing a button appear on screen and being able to double-click it to write the code that runs when it's clicked was revelatory.
- Simple syntax - VB6's BASIC-derived syntax was readable and forgiving.
If username <> "" Thenmade intuitive sense even to a complete beginner. No curly braces, no semicolons, no pointer arithmetic. - The Winsock control - This was the killer feature for progz. The Microsoft Winsock Control (MSWINSCK.OCX) was an ActiveX component that provided TCP/IP and UDP socket access through a simple, event-driven interface. You could establish a network connection, send data, and receive responses with just a few lines of code. For progz authors, this was everything - it was the bridge between VB6's friendly interface and the raw network access needed to exploit chat protocols.
- Compile to .exe - VB6 could compile projects into standalone Windows executables. No runtime installation required (well, the VB6 runtime DLLs needed to be present, but they were on most Windows machines by the late '90s). This meant progz could be distributed as single .exe files - download, double-click, and you're booting people.
- Abundant tutorials - The VB6 community was massive, and tutorials were everywhere. Planet Source Code, VBForums, and dozens of other sites had thousands of code examples. Progz-specific tutorials circulated on Geocities pages and IRC channels, walking aspiring script kiddies through the process step by step.
The Anatomy of a VB6 Prog
If you ever used a prog, you'd recognize the look instantly. The default VB6 form had a distinctive appearance: a gray background (the default Windows control color), 3D-beveled buttons, and the system font. Most progz authors didn't bother customizing the appearance beyond changing button captions and adding a few labels in colored fonts.
A typical Yahoo booter's VB6 code looked something like this:
' Yahoo Booter - VB6 Pseudocode (simplified)
Private Sub cmdBoot_Click()
Dim targetUser As String
targetUser = txtTarget.Text
If targetUser = "" Then
MsgBox "Enter a username to boot!", vbExclamation
Exit Sub
End If
' Connect to Yahoo's chat server
Winsock1.RemoteHost = "cs.yahoo.com"
Winsock1.RemotePort = 5050
Winsock1.Connect
' Send malformed YMSG packet
Dim packet As String
packet = BuildYMSGPacket(targetUser)
' Send the boot packet repeatedly
Dim i As Integer
For i = 1 To Val(txtCount.Text)
Winsock1.SendData packet
DoEvents ' Keep the UI responsive
Next i
lblStatus.Caption = "Booting " & targetUser & "..."
End SubThe actual exploit packets were more complex, of course, but the structure was always the same: connect to Yahoo's server, construct a malformed packet, send it repeatedly. The DoEvents call was a VB6 classic - it yielded control back to the Windows message loop so the UI wouldn't freeze during the send loop. Every VB6 programmer learned about DoEvents the hard way.
Learning to Code Through Chaos
Here's the thing that's easy to dismiss but genuinely important: progz taught a generation of kids to program. Not through formal education, not through textbooks, not through computer science classes (most schools didn't offer them yet). Through the desire to build tools that did cool (if destructive) things.
The learning path was remarkably consistent:
- Download and use progz - Pure consumption. You download someone else's booter and use it.
- Get curious - You wonder how it works. You right-click the .exe and realize you can't see the source code.
- Discover VB6 - Someone on IRC or a forum mentions Visual Basic. You pirate a copy (nobody bought software in the '90s underground).
- Follow tutorials - You find a "How to make a Yahoo Booter" tutorial on a Geocities page. You follow it step by step, not understanding most of what you're typing.
- Modify existing code - You get someone's source code and start changing things. Different colors, different messages, your handle in the title bar.
- Write your own - Eventually, you understand enough to write a prog from scratch. You've learned variables, loops, conditionals, functions, network sockets, and string manipulation. You are, whether you realize it or not, a programmer.
- Branch out - The skills transfer. You start building other things - websites, games, utilities. The progz were the gateway, but the skills were real.
It's impossible to overstate how many careers in technology started with VB6 and progz. Talk to software developers, security researchers, and sysadmins who grew up in the late '90s, and a surprising number will sheepishly admit that their first program was a Yahoo booter or a chat flooder. The motivation was juvenile, but the education was real. VB6 taught an entire generation the fundamentals of event-driven programming, network communication, and software distribution - lessons that transferred directly to legitimate careers.
6. The Distribution Network: Geocities, Angelfire, and the Dark Web Before the Dark Web

Before cloud hosting and CDNs, the progz distribution network ran on free web hosts with 15MB storage limits.
Progz needed a distribution channel, and in the late '90s, that channel was the free web hosting ecosystem. Geocities, Angelfire, Tripod, and FortuneCity - these were the platforms that gave anyone with a web browser the ability to create a website for free. And the progz scene exploited them relentlessly.
The Prog Site Aesthetic
If you've ever seen a parody of a '90s website, you've seen a prog site. The aesthetic was so consistent it might as well have been a template:
- Black background - Always. Without exception. Black was "hacker."
- Green text - Lime green, specifically.
color="#00FF00". The Matrix hadn't come out yet when the trend started (it was more of a terminal/DOS callback), but after 1999, every prog site claimed Matrix inspiration. - Animated GIFs - Flaming skulls, spinning globes, "Under Construction" signs, animated email icons, and the ubiquitous hit counter. The more animated GIFs, the more "elite" the site.
- MIDI background music - Many prog sites auto-played MIDI files. Metallica's "Enter Sandman" and the Mortal Kombat theme were perennial favorites.
- Visitor counters - Every prog site had a hit counter, usually from a service like WebCounter or Digits.com. A high hit count was a badge of honor.
- Guestbooks - Where visitors left comments. Guestbooks on prog sites were a mix of "cool site bro" and "your progz suck, mine are better."
- Webrings - Remember webrings? Prog sites were often part of webrings that linked related sites together. The "Yahoo Progz Webring" connected dozens of sites.
- "Best Viewed In" badges - "Best Viewed in Netscape Navigator 4.0 at 800x600 resolution." These badges were everywhere.
The site names were equally predictable: DarkSide Progz, Elite Yahoo Tools, Shadow's Boot Page, xXx Hacker's Paradise xXx, The Underground, Digital Chaos. Every site claimed to have the "best" and "most powerful" progz, and every site warned visitors that the tools were "for educational purposes only" - a legal disclaimer that fooled absolutely nobody.
The Download Experience
Downloading a prog in 1998 was an adventure in itself:
- You'd find a prog site through a link on IRC, a Yahoo Chat room, or another prog site's links page.
- You'd navigate through the site's labyrinthine structure - prog sites loved nested pages with names like "enter.html," "main.html," "progz.html," and "secret.html."
- You'd find the download section, which listed progz with brief descriptions and download links.
- The download link pointed to a .zip or .rar file hosted on the same Geocities account (or sometimes on a separate "mirror" account because Geocities had bandwidth limits).
- You'd download the archive - usually 200KB to 2MB - which at 56k took anywhere from 30 seconds to several minutes.
- You'd extract the archive using WinZip or WinRAR (both pirated, naturally).
- Your antivirus would immediately flag the .exe as a threat. You'd disable the antivirus or add an exception.
- You'd run the prog and hope for the best.
The Antivirus Cat-and-Mouse
The relationship between progz and antivirus software was a constant arms race. Norton Antivirus, McAfee, and AVG would flag progz as malicious - and they were often right to do so, since many progz contained trojans. But even "clean" progz got flagged because their behavior (sending mass network packets, automating login attempts, flooding connections) matched malware signatures.
Progz authors responded with various evasion techniques:
- Packers and crypters - Tools like UPX, ASPack, and custom crypters compressed and obfuscated the executable, changing its signature enough to evade detection.
- FUD (Fully UnDetectable) - The holy grail. A prog that was "FUD" wouldn't be flagged by any major antivirus. Achieving FUD status was a point of pride for prog authors, and "FUD" was a major selling point in prog descriptions.
- Source code distribution - Some authors distributed source code instead of (or alongside) compiled executables, arguing that users could compile it themselves and verify there were no trojans. This only worked for users who had VB6 installed, which limited the audience.
- Binder programs - Tools that combined multiple executables into a single file. Progz authors used binders to attach trojans to legitimate-looking progz. But "clean" prog authors also used binders to package their prog with required DLLs.
The result was a perpetual cycle: antivirus companies would update their signatures, progz authors would update their evasion techniques, and users would disable their antivirus entirely because it kept blocking the tools they wanted to use. The security implications were catastrophic - an entire generation of teenagers running unprotected Windows 98 machines with dozens of downloaded executables of unknown provenance. It's a miracle any of our computers survived.

Source code was currency in the progz underground.

The command line: where real hackers lived.

Every prog started as lines of code in a VB6 IDE.

mIRC banner from mirc.com (archived 2000)

mIRC's CNET award - legitimacy for the underground
7. IRC and the Hacker Hierarchy: Where the Real Action Was

IRC was the dark heart of the hacker underground - no corporate oversight, no rules, no mercy.
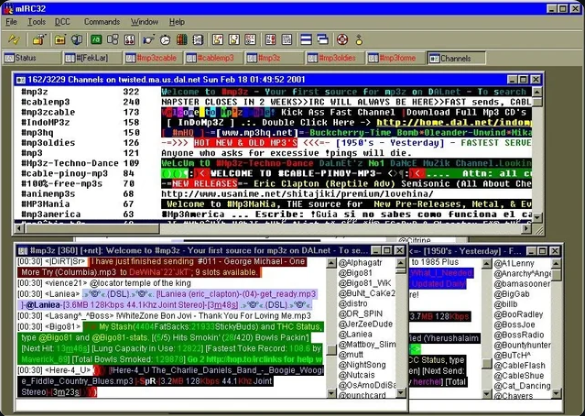
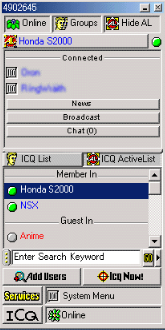
mIRC32 on DALnet, circa 2001 - channel list showing MP3 trading rooms (Mp3z, 8cablemp3, Mp3zable), colored text spam, Napster references, and the chaotic multi-window interface that defined IRC culture. This is what the scene actually looked like.
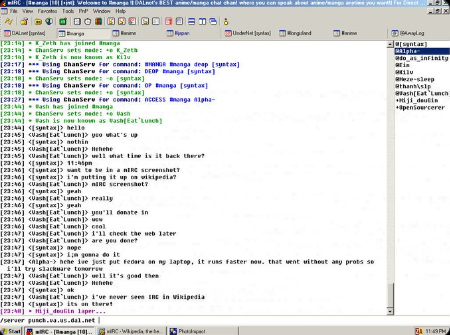
An actual mIRC chat session - channel ops being set, mode changes, nick changes, and real conversation. Note the channel list on the right, the classic mIRC toolbar, and the raw IRC protocol visible in the chat.
If Yahoo Chat was where progz were used, IRC (Internet Relay Chat) was where they were made. IRC was the backbone of the hacker underground in the late '90s, and it operated on a completely different level than the consumer chat platforms.
The IRC Landscape
IRC was a decentralized network of servers organized into networks. The major networks each had their own culture:
- EFnet (Eris Free Network) - The oldest and most anarchic. No channel registration, no nickname services. If you wanted to keep a channel, you had to defend it. EFnet was where the serious hackers and warez groups operated.
- DALnet - More user-friendly, with nickname and channel registration services (NickServ and ChanServ). DALnet was popular with the progz crowd because it was easier to maintain a persistent presence.
- Undernet - Similar to DALnet but with its own community. Known for its channel service bot, "X."
- QuakeNet - Originally built for the Quake gaming community, but it grew into a general-purpose network.
- IRCnet - Popular in Europe. Had its own distinct culture.
The client of choice was mIRC, created by Khaled Mardam-Bey. mIRC was shareware (another program nobody paid for), and it was far more than a simple chat client. mIRC had its own scripting language - mIRC Script - that was powerful enough to build bots, automate tasks, and create complex interactive systems. mIRC scripting was another gateway to programming for '90s teenagers.
The Hierarchy
The hacker underground had a rigid, if informal, hierarchy. Where you fell on this ladder determined your status, your access to tools and information, and how much respect (or contempt) you received:
Level 1: Lamers / n00bs
The bottom of the food chain. Lamers didn't even use progz - they just hung out in hacker-themed chat rooms and pretended to know things. They asked obvious questions ("how do I hack hotmail?"), used "hacker" screen names, and were universally mocked. The term "lamer" was the worst insult in the scene - worse than any profanity.
Level 2: Script Kiddies
Script kiddies used progz and scripts they didn't write and didn't understand. They could boot people from Yahoo Chat and flood IRC channels, but they couldn't explain how their tools worked. They were the foot soldiers of the progz scene - numerous, noisy, and not particularly respected by anyone above them on the ladder. The term "script kiddie" was coined specifically to describe this group, and it remains in use in cybersecurity to this day.
Level 3: Coders
Coders wrote their own tools. They understood the protocols, the exploits, and the code. A coder who released a popular prog earned significant respect in the scene. Coders were the artisans of the underground - they might not discover new exploits, but they could weaponize known ones into usable tools. Most coders worked in VB6 or Delphi, with the more ambitious ones using C/C++.
Level 4: Hackers
Real hackers found their own exploits. They reverse-engineered protocols, discovered buffer overflows, and understood systems at a deep level. Hackers looked down on the progz scene as juvenile (which it was), but many of them had started as script kiddies themselves. The line between "coder" and "hacker" was blurry - it was less about specific skills and more about whether you discovered vulnerabilities or just exploited known ones.
Level 5: Elite
The elite were the apex predators. They ran botnets (networks of compromised computers), discovered zero-day vulnerabilities, and operated at a level that was genuinely dangerous. Some were involved in serious cybercrime - credit card fraud, corporate espionage, infrastructure attacks. Others were white-hat researchers who would go on to found security companies. The elite rarely interacted with the progz scene directly, but their exploits and techniques trickled down through the hierarchy.
mIRC Scripting: The Other Gateway Drug
mIRC's built-in scripting language was surprisingly powerful. You could write scripts that:
- Automated channel management (auto-op, auto-kick, auto-ban)
- Created interactive bots (trivia bots, quote bots, seen bots)
- Built custom interfaces with dialogs and menus
- Performed network operations (DCC file transfers, raw socket connections)
- Implemented protection scripts that detected and responded to floods and attacks
mIRC scripts were distributed as .mrc files and shared on IRC channels and websites. Like progz, they ranged from useful utilities to outright malicious tools. "War scripts" were mIRC scripts designed for channel warfare - they automated flooding, cloning (joining with multiple nicknames), and takeover attempts.
For many people, mIRC scripting was an even more accessible entry point to programming than VB6. You didn't need to install a development environment - mIRC itself was the IDE. You could write a script, test it immediately in a live IRC session, and iterate in real time. The feedback loop was instant and addictive.
IRC Bots and Botnets
IRC bots were automated programs that connected to IRC and performed tasks. Legitimate bots managed channels, provided information, and facilitated file sharing. But the progz scene's contribution to bot culture was the botnet - a network of compromised computers, each running a bot that connected to a secret IRC channel and waited for commands.
Botnets were controlled through IRC because the protocol was perfect for command-and-control: it was real-time, it supported private channels, and it was decentralized enough to be resilient. A botnet operator could type a command in an IRC channel, and hundreds or thousands of compromised machines would execute it simultaneously. The most common use was DDoS attacks (Distributed Denial of Service) - directing the entire botnet to flood a target with traffic, overwhelming their connection.
The progz scene was both a source and a target of botnets. Progz bundled with trojans like SubSeven or Back Orifice recruited new bots for the operator's network. And botnets were used to DDoS rival prog crews, take down competing prog sites, and attack IRC channels. It was an ecosystem of mutual exploitation.

AIM promotional graphic from aim.com - archived from 2002
8. The AOL Scene: America's First Hackers

For millions of Americans, AOL wasn't just an ISP - it was the internet itself. And it was hilariously easy to exploit.
Before Yahoo Chat dominated the progz scene, there was AOL - America Online. And the AOL hacking scene was, in many ways, the direct ancestor of everything that followed.
AOL: The Walled Garden
AOL was unique among internet services because it wasn't really an ISP in the traditional sense. It was a walled garden - a self-contained online world with its own chat rooms, message boards, email, news, and content. When you connected to AOL, you weren't connecting to the open internet (at least not initially). You were connecting to AOL's proprietary network, which happened to also provide internet access.
This made AOL simultaneously the most popular and the most exploitable platform of the era. Its proprietary client software (the AOL Desktop) was a massive, bloated application that handled everything from dialing the modem to rendering web pages. And it was riddled with vulnerabilities.
AOHell: The Legend
AOHell was the progz scene's Rosetta Stone. Created in 1995 by a teenager using the handle "Da Chronic," AOHell was an all-in-one AOL exploitation tool that could:
- Phish accounts - Generate fake "AOL Staff" instant messages asking users for their passwords. The messages looked official enough to fool many users, especially those new to the internet.
- Punt users - Disconnect other AOL users from the service by exploiting protocol weaknesses.
- Mail bomb - Flood AOL email accounts with thousands of messages.
- Generate fake credit cards - Create credit card numbers that passed AOL's validation checks, allowing the creation of free accounts. (AOL required a credit card for registration.)
- IM bomb - Flood a user's AIM (AOL Instant Messenger) with rapid-fire messages, freezing their client.
- Chat room tools - Flood chat rooms, create scrolling text, and disrupt conversations.
AOHell was revolutionary not because its individual features were technically impressive, but because it packaged everything into a single, easy-to-use tool. Before AOHell, exploiting AOL required technical knowledge. After AOHell, anyone could do it. It democratized disruption - and in doing so, it created the template that every subsequent prog would follow.
AOL responded aggressively, updating their software to patch the exploits AOHell used. But the cat-and-mouse game had begun. New tools emerged to replace AOHell: Fate X, AOL4Free, Happy Hardcore, and dozens of others. Each new AOL version patched old exploits and introduced new ones. The cycle continued for years.
The Phishing Epidemic
AOL was ground zero for phishing - the practice of tricking users into revealing their passwords by impersonating a trusted authority. The technique was devastatingly simple:
- Create an AOL screen name that looked official: "AOL Staff," "AOL Admin," "AOL Security."
- Send an instant message to a target: "Hi, this is AOL Technical Support. We're updating our records and need to verify your account. Please reply with your password."
- Wait for the target to reply with their password.
- Log into their account, change the password, and use the account for your own purposes.
It sounds absurd, but it worked constantly. Remember, many AOL users in the mid-'90s had never used a computer before. They didn't know that a legitimate company would never ask for their password via instant message. They saw "AOL Staff" and trusted it. The success rate was shockingly high.
Phished accounts were valuable commodities. They could be used to create new screen names (AOL allowed multiple screen names per account), access premium content, and - most importantly - serve as disposable identities for further hacking. When the account's real owner reported the compromise, AOL would lock the account, and the hacker would simply move on to the next phished account.
AIM: The Instant Messenger Wars
AIM (AOL Instant Messenger) deserves its own mention. While AOL's chat rooms were the primary target of the early progz scene, AIM became the dominant instant messaging platform of the late '90s and early 2000s - used by millions of people who had no connection to AOL itself.
AIM had its own set of exploits and progz:
- IM bombers - Sent hundreds of messages per second to a target, freezing their AIM client
- Profile exploits - Malicious HTML in AIM profiles that could crash the viewer's client or redirect them to phishing pages
- Direct connect exploits - AIM's direct connection feature (for file transfers and direct IM) exposed users' IP addresses, making them vulnerable to further attacks
- Warning wars - AIM had a "warn" feature that increased a user's warning level. At high warning levels, the user was rate-limited or disconnected. Progz could automate warning to quickly max out a target's warning level.
The AIM buddy list was the social network before social networks. Your buddy list was your online identity - who you talked to, who you avoided, who you had a crush on. AIM away messages were the precursor to status updates. And AIM progz could disrupt all of it.

Trillian award

Trillian in PC World

Trillian on ABC News
9. The Culture: Skulls, Handles, and the Hacker Aesthetic

The Matrix (1999) didn't create the hacker aesthetic - but it crystallized it into something iconic.

The glow of a CRT in a dark room: the universal symbol of late-night hacking.
The progz scene wasn't just about tools - it was a culture. It had its own aesthetic, its own language, its own values, its own heroes, and its own mythology. Understanding the culture is essential to understanding why progz mattered and why they left such a lasting mark on the people who were part of the scene.
The Aesthetic
The visual language of the late-'90s hacker underground was unmistakable and remarkably consistent across platforms, countries, and communities:
- Black and green - The dominant color scheme. Black backgrounds with green text, inspired by old-school terminal displays and later reinforced by The Matrix's iconic "digital rain." Red was the secondary accent color - used for warnings, emphasis, and anything meant to look dangerous.
- Skulls - Everywhere. Flaming skulls, pixelated skulls, ASCII skulls, 3D-rendered skulls. The skull was the universal symbol of the hacker underground. Every prog site had at least one skull GIF. Many had dozens.
- ASCII art - Text-based art was a core part of the culture. Elaborate ASCII banners announced crew names, prog releases, and website headers. Creating good ASCII art was a respected skill. NFO files (information files distributed with warez releases) were works of ASCII art in themselves.
- The Matrix - After the film's release in March 1999, the hacker aesthetic became permanently fused with Matrix imagery. Green cascading code, black leather, sunglasses, and Neo quotes became ubiquitous. "There is no spoon" appeared on every other prog site.
- "Hacked by" pages - Website defacement was a rite of passage. When a hacker compromised a website, they'd replace the homepage with a "Hacked by [handle]" page - black background, green text, skull GIF, and a message taunting the site's administrator. These defacements were collected and archived on sites like Attrition.org.
- L33tspeak - The substitution cipher of the underground. Letters replaced with numbers and symbols: A=4, E=3, I=1, O=0, T=7, S=5. "Elite" became "3l1t3." "Hacker" became "h4x0r." "Programs" became "pr0gz." L33tspeak served both as an in-group identifier and as a (futile) attempt to evade text-based content filters.
Handles and Identity
Nobody used their real name. Everyone had a handle - an alias that served as their identity in the underground. Handles were chosen with care and defended fiercely. A good handle was short, memorable, and vaguely threatening: DarkLord, PhantomX, CyberGhost, NightShade, Viper, Reaper. Handles with "x" were especially popular - xXDarkXx, XeNoN, Xploit.
Your handle was your reputation. If you released a popular prog under a handle, that handle became known. If you got caught doing something embarrassing (like getting your own machine trojaned), that handle was tainted. Some people cycled through handles to escape bad reputations. Others maintained the same handle for years, building a legacy.
Handles were also the source of endless drama. Name disputes - two people claiming the same handle - could escalate into full-scale wars involving DDoS attacks, account theft, and website defacement. The concept of "owning" a name in a space with no central authority was inherently contentious.
Crews and Cliques
Progz authors and users organized into crews - informal groups that collaborated on tools, shared exploits, and competed for reputation. Crew names followed the same aesthetic as everything else: Dark Side Crew, Digital Chaos, Shadow Elite, Phantom Force, Underground Kings.
Crews had their own IRC channels, their own websites, and their own internal hierarchies. Being accepted into a respected crew was a status symbol. Crews competed by releasing better progz, defacing each other's websites, and engaging in IRC channel wars. The rivalries were intense and personal - remember, these were teenagers with fragile egos and unlimited free time.
The Warez Connection
The progz scene overlapped heavily with the warez scene - the underground distribution of pirated software, games, movies, and music. Warez groups operated on IRC and FTP servers, releasing "cracked" versions of commercial software with copy protection removed.
The connection was natural: progz users needed pirated copies of VB6 and Delphi to write their tools. They needed pirated copies of WinZip and WinRAR to distribute them. They needed pirated copies of Norton Antivirus to test whether their progz were detected. The entire ecosystem ran on pirated software.
Warez culture contributed several elements to the progz scene:
- NFO files - Text files with ASCII art headers that accompanied warez releases. Progz adopted the same format for their release notes.
- Keygens - Key generators that produced valid serial numbers for commercial software. Keygens were famous for their chiptune music - many keygens played elaborate electronic music while generating keys. The keygen music scene became a subculture in its own right.
- Cracktros - Animated intros that played before cracked software launched, crediting the cracking group. Some progz included similar intros.
- The release race - Warez groups competed to be the first to release a cracked version of new software. Progz crews adopted the same competitive mentality, racing to release tools for newly discovered exploits.
Movies That Defined the Aesthetic
Two films shaped the hacker underground's self-image more than any others:
Hackers (1995) - Directed by Iain Softley, starring Jonny Lee Miller and Angelina Jolie. The film was technically absurd (3D file systems, hacking via rollerblading), but it captured the feeling of the scene perfectly: young outsiders using technology to fight the system, with a killer soundtrack and a rebellious attitude. Every hacker wanted to be Crash Override or Acid Burn. The film's tagline - "Their only crime was curiosity" - became an unofficial motto of the underground.
The Matrix (1999) - The Wachowskis' masterpiece didn't just influence the hacker aesthetic - it became the hacker aesthetic. The green-on-black color scheme, the concept of reality as a hackable system, the idea that knowledge of how things "really work" sets you apart from the masses - all of this resonated deeply with the progz scene. Neo was the ultimate hacker fantasy: a programmer who discovers that the entire world is code, and that he can rewrite it.
Other influential media included:
- Sneakers (1992) - A more realistic take on hacking and social engineering
- WarGames (1983) - The original hacker film, still revered in the '90s
- The Hacker Manifesto (1986) - Written by "The Mentor" after his arrest, this short essay ("The Conscience of a Hacker") was treated as scripture in the underground. "My crime is that of curiosity" was quoted endlessly.
- Swordfish (2001) - Arrived at the tail end of the era, featuring Hugh Jackman as a hacker. Ridiculous but entertaining.
- 2600: The Hacker Quarterly - The print magazine of the hacker community. Finding a copy at Barnes & Noble felt like discovering a secret society's newsletter.
10. The Legacy: From Script Kiddies to Security Professionals

Many of today's senior developers and security researchers got their start in the progz scene. The tools were juvenile, but the skills were real.
The progz scene died slowly, then all at once. Yahoo patched the worst YMSG exploits. AOL overhauled its security. IRC networks implemented better flood protection and channel services. Windows XP's built-in firewall (enabled by default in SP2) made many network-level attacks harder. And most importantly, the social landscape shifted: MySpace, then Facebook, then Twitter replaced chat rooms as the primary social spaces of the internet. By 2005, Yahoo Chat was a ghost town. By 2012, it was officially shut down.
But the progz scene's legacy extends far beyond the tools themselves. It shaped careers, influenced cybersecurity, and left cultural fingerprints that are still visible today.
The Career Pipeline
Here's the dirty secret of the tech industry: a lot of successful technology professionals got their start in the progz scene. Not all of them will admit it, but the pipeline was real and significant:
- Software developers - Kids who learned VB6 to build booters went on to learn C++, Java, Python, and JavaScript. The fundamentals they picked up - variables, loops, functions, event-driven programming, network sockets - transferred directly to legitimate development.
- Security researchers - The progz scene was, in essence, an informal education in offensive security. Understanding how exploits work, how protocols can be abused, and how systems fail under adversarial conditions is exactly what penetration testers and security researchers do professionally.
- System administrators - Running IRC bots, managing servers, and understanding network protocols prepared many progz-scene veterans for careers in system administration and DevOps.
- Entrepreneurs - The hustle of the progz scene - building tools, building an audience, competing for reputation - was entrepreneurship in miniature. Several successful tech companies were founded by people who cut their teeth in the underground.
The irony is rich: a scene built on disruption and destruction produced a generation of builders. The same curiosity that drove a 14-year-old to figure out how to crash a Yahoo Chat room drove a 24-year-old to figure out how to build a scalable web application, and a 34-year-old to figure out how to secure a corporate network.
The Cybersecurity Connection
The modern cybersecurity industry owes a significant debt to the progz scene, whether it acknowledges it or not. Several direct connections:
- CTF competitions - Capture The Flag events, where teams compete to find and exploit vulnerabilities in controlled environments, are the legitimate descendant of the progz scene's competitive hacking culture. The skills are the same; the context is legal and constructive.
- Bug bounty programs - Companies now pay hackers to find vulnerabilities in their systems. This is essentially what progz authors did for free (and without permission) in the '90s. The difference is consent and compensation.
- Red teaming - Professional red teams simulate attacks against organizations to test their defenses. The mindset - "how can I break this?" - is identical to the progz scene's approach to chat room protocols.
- Social engineering awareness - The phishing techniques pioneered on AOL are now the primary vector for cyberattacks worldwide. The progz scene was an early laboratory for social engineering, and the lessons learned (on both sides) inform modern security training.
What Killed the Scene
The progz scene didn't die from a single cause - it was a convergence of factors:
- Platform patches - Yahoo, AOL, and IRC networks gradually fixed the vulnerabilities that progz exploited. Each patch rendered existing tools obsolete, and the effort required to find new exploits increased over time.
- Better security - Windows XP SP2's firewall, improved antivirus software, and NAT routers made end-user systems harder to attack. The era of directly exploitable home computers was ending.
- Social media migration - Chat rooms were replaced by social networks. MySpace (2003), Facebook (2004), and Twitter (2006) offered richer social experiences with better moderation. The chat room as a social space became obsolete.
- Legal consequences - As law enforcement caught up with internet crime, the risks of participating in the progz scene increased. High-profile arrests and prosecutions sent a chilling message through the community.
- Growing up - The progz scene's participants were teenagers. They grew up, went to college, got jobs, and moved on. The thrill of booting someone from a chat room loses its appeal when you're 22 and have rent to pay.

The servers got bigger, the security got better, and the wild west was tamed.

Today's internet is sleeker, safer, and infinitely less chaotic. Whether that's entirely a good thing is debatable.
A Lost World
The internet of the late 1990s is gone. Not just changed - gone. The chat rooms are closed. The Geocities pages are deleted (though the Internet Archive preserved some). The IRC channels are empty. The progz sites are dead links. The culture exists only in the memories of the people who were there and in scattered archives across the web.
And that's worth mourning, even if the scene was often toxic, juvenile, and harmful. Because it was also creative, educational, and alive in a way that today's internet rarely is. The progz scene was a place where teenagers taught themselves to code, explored the boundaries of technology, and discovered that the systems they used every day were not immutable - they could be understood, manipulated, and even broken.
That spirit of curiosity, of refusing to accept systems at face value, of wanting to understand how things really work - that's the hacker ethos. And it didn't die with Yahoo Chat. It lives on in every security researcher who finds a zero-day, every open-source contributor who patches a vulnerability, every developer who asks "but what happens if I send this instead?"
The progz are gone. The spirit endures.
Bonus: Timeline of the Progz Era
| Year | Event |
|---|---|
| 1993 | AOL opens internet access to its subscribers. Chat rooms explode in popularity. |
| 1995 | AOHell released. The movie Hackers hits theaters. The hacker aesthetic is born. |
| 1996 | Yahoo Chat launches. Geocities becomes the go-to free web host. IRC networks peak in popularity. |
| 1997 | AOL Instant Messenger (AIM) launches. Back Orifice released by Cult of the Dead Cow. |
| 1998 | Visual Basic 6 released. Yahoo Chat progz scene explodes. SubSeven trojan appears. The golden age begins. |
| 1999 | The Matrix released. Napster launches. The progz scene reaches peak activity. Green-on-black becomes the law. |
| 2000 | Yahoo begins patching major YMSG exploits. The dot-com bubble bursts. The scene starts to fragment. |
| 2001 | Windows XP released. AIM dominates instant messaging. Progz scene shifts focus to IM exploits. |
| 2002 | Yahoo overhauls chat protocol. Many classic progz stop working. Geocities begins its decline. |
| 2003 | MySpace launches. Social networking begins replacing chat rooms. The migration begins. |
| 2004 | Facebook launches. Windows XP SP2 enables firewall by default. The progz era is effectively over. |
| 2009 | Yahoo acquires and then shuts down Geocities. Millions of prog sites vanish forever. |

The cursor blinks. The modem is silent. The chat rooms are empty. But the code - and the curiosity - lives on.
🕰️ See it yourself on the Wayback Machine: